Security is high on people’s agenda when choosing a host to take care of their WordPress website. Poor security can result in malicious attacks and damaging code injections. In the worst case, a hack renders your website as nonfunctional.
At Pressidium we’d like to ease your WordPress security frustrations. We’ve scoured hundreds of security related articles. Combine them with our expert experience, and you have a fountain of security knowledge. Today you’ll learn how each of our features, effectively secures your WordPress website.
Understanding Your Environment
To understand your site’s security, it’s important to look at Pressidium’s Enterprise environment setup.
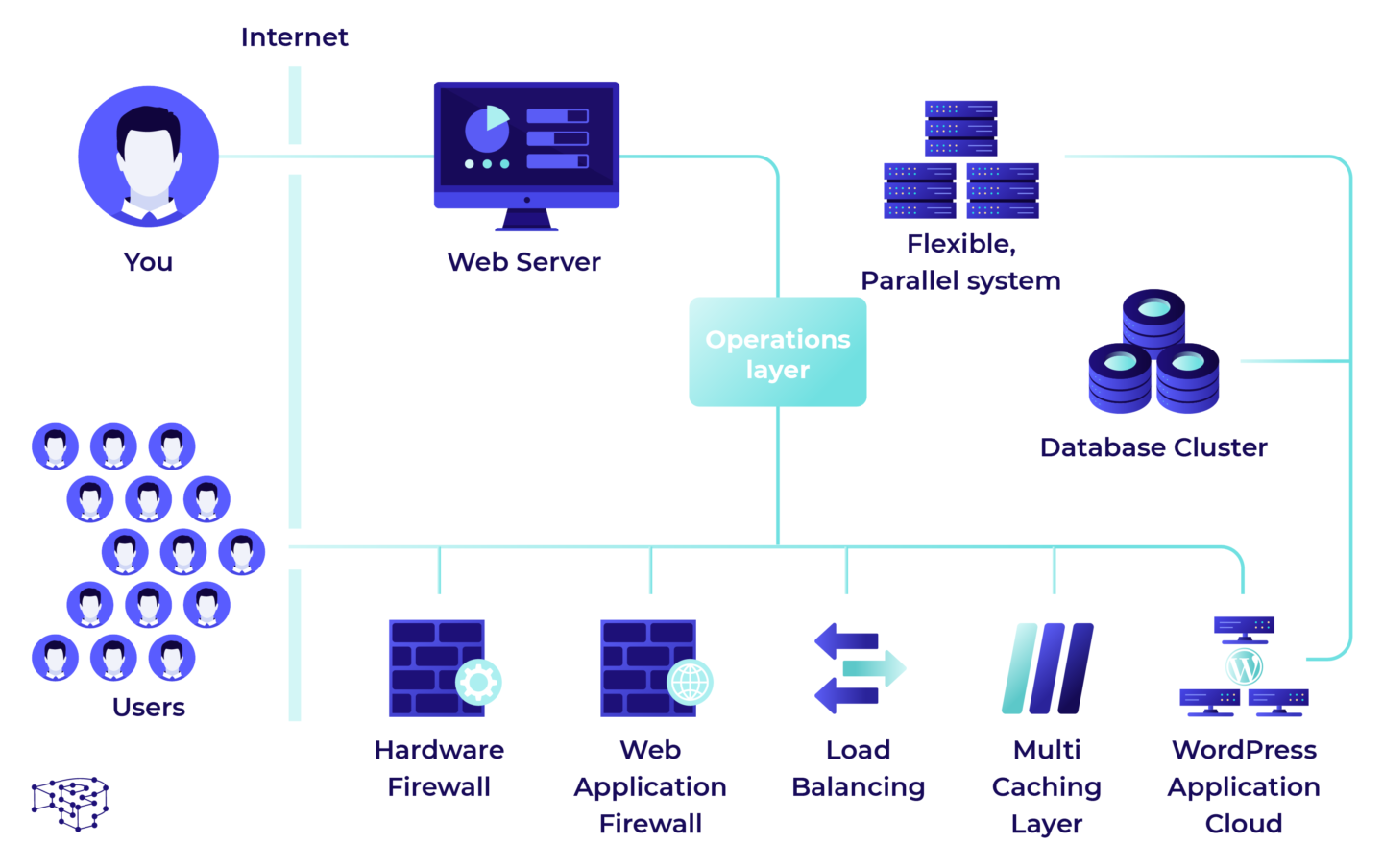
An Enterprise hosting environment such as this forms the basis by which your website can function. But how is all this kept secure? Today we will shed some light on this often confusing topic and try to demystify it a little.
How Our Hosting Keeps WordPress Secure?
At Pressidium we focus on Managed WordPress hosting. We know WordPress inside and out, so it made sense to pool our knowledge into this area. Yet secure WordPress hosting and protecting our customers installations, is something we’re always evaluating. As sophisticated malicious activities increase, so too must we stay ahead of the game.
To do this we’ve implemented many layers of security based on industry best practices. An example of this is Managed WordPress Updates. This ensures you’re always using the most stable, therefore secure, version of WordPress there is on your hosted installations.
For plugin and theme updates, these will occur only if they pose a security threat. We won’t update them out of the blue either. We’ll only do this with your express permission.
If you need to keep hold of that out-of-date plugin but don’t want your site hacked, we can help. We use what’s known as ‘Virtual Patching’ in our Web App Firewall (WAF). The WAF intercepts incoming attacks due to a known vulnerability. This allows us to protect your site, even if it’s outdated.
Try our Award-Winning WordPress Hosting today!
To scan for exploits, malware and known security issues, we also implement server side scanning with Maldet and WPVulnDB. Maldet is software designed to detect malware specifically for hosting environments. This is different to other anti-virus programs. They only search for Operating System level trojans and traditional file-infecting viruses. Instead we scan against known vulnerabilities, the sources of which are from maintained databases.
We even go as far as protecting you against brute-force attacks too. This is where a hacker throws sequences of key combinations at your website, to find the right password. The Pressidium® Pinnacle Platform detects these attacks and blocks the IP address from our firewall layer.
Our Web Application Firewall has a design built around the Varnish Security Firewall concept. Using OWASP rules and filters, the firewall prevents attack vectors from reaching your installation. Should a (D)DoS attack occur, the attacking IP will receive a throttling measure. This counter measure slows down new connections from the malicious IP. It then overloads their CPU and resource usage. This makes it difficult to carry on with their attack.
With the ability to identify common attack trends we can protect customers from them. Should attacks persist, we can block the IP and use our geo-blocking features. This prevents entire countries from accessing a website if needed.
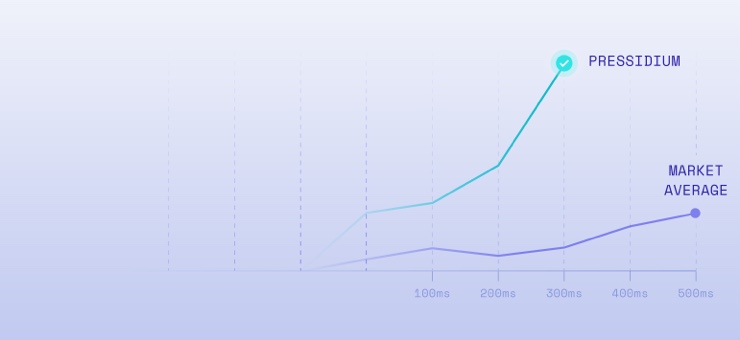
There is of course a disadvantage to all the above network filtering. We lose 50ms-100ms from our speed. We think it’s a fair compromise to make when it comes to secure WordPress hosting, as we’re sure you’ll agree.
Connecting to Our Servers
When connecting to our servers, you do so in a chroot-ed OS environment. This means your account’s isolated and partitioned from other accounts. Your account’s php processes exist in a logical silo or partition. Here they have access only to your files and your resources. Your environment can’t “see” the resources of other accounts and other accounts can’t “see” yours. This is important to understand. If someone else’s account becomes compromised they’ll never have access to your data.
You can also access your files via our Secure FTP service. Only your personal account is given access in this instance. Since we provide your server management, there’s also no root access. All this is contained within an SSL enabled Control Panel. We call this your customer portal and it provides an overview of your account.
Do I need a Systems Administrator?
In conventional hosting environments you’re likely used to setting up everything on your own. Configuring and administering your install is likely your task too. This can be a lengthy and time-consuming job. This is especially true if your knowledge is limited.
On conventional VPS or Dedicated Servers you’ll also need to administer your operating system. Knowing your way around Linux, MySql, Apache & Nginx, PHP-FPM is a must. This is all too often overwhelming for most. It usually leads to your site going down or being hacked due to the lack of technical skill. Not to mention the time and effort required to keep everything in tip-top shape.
With our managed hosting, all upkeep is managed by our team of DevOps engineers. This includes patches, upgrades and updates, while keeping possible compatibility issues in mind.
N-Tier Enterprise Architecture: Security by Design
By design Pressidium’s Enterprise Architecture, increases the level of security on our platform. This is because each component is hidden behind a separated layer of servers. Each of these server layers are behind yet another separate layer of internal firewalls. In essence all our application and database servers are difficult to compromise. This is because they’re not being directly exposed to the internet.
This architecture makes it difficult for attackers to create network footprints and discover vulnerabilities. All critical components are hidden inside secured internal private networks. These in turn are monitored closely for malicious traffic.
What If My Site Gets Hacked?
In the unlikely event that your site does become hacked, we’ll fix it for you, free of charge. We’ll identify the exploited resource and fix that too. We’ll try to understand how the exploit came to occur, to prevent it in the future.
But we’d like to stress that this is unlikely to happen. Our entire enterprise WordPress hosting platform has a design with security at it’s heart. Utilizing security best practices it’s also made with the best technology on the market. Without this level of attention to detail, we’d just be yet another wordpress host.
We bring to the table all this and so much more. Your security is our security. As engineers we create elegant solutions for some of the most complex tasks. That’s what you get with Pressidium. All the complexities of a secure hosting environment, combined into a single, elegant solution.
Start Your 14 Day Free Trial
Try our award winning WordPress Hosting!